In the modern enterprise landscape, technology risk is no longer an isolated IT concern. It permeates every layer of organizational strategy, from daily operations to long-term viability. Organizations often struggle to connect high-level business goals with the specific technical controls required to protect them. This disconnect creates vulnerabilities that can lead to financial loss, reputational damage, or regulatory non-compliance. To bridge this gap, leaders are turning to structured frameworks that translate abstract motivations into concrete risk management strategies. One such framework is the Business Motivation Model (BMM). By leveraging the BMM, enterprises can align their technological investments directly with their core motivations, ensuring that risk mitigation is not an afterthought but a foundational element of strategic execution.
This guide explores how to utilize Business Motivation Model assessments to identify, analyze, and mitigate technology risks. We will move beyond generic security checklists and examine the underlying drivers of risk. By understanding what the business actually wants and needs, risk professionals can prioritize controls that deliver genuine value rather than just ticking compliance boxes.
🧩 Understanding the Business Motivation Model Fundamentals
The Business Motivation Model (BMM), developed by the Object Management Group (OMG), provides a standardized way to model the business environment. It is designed to clarify the relationship between business objectives and the means to achieve them. While often used for strategic planning, its structure is equally powerful for risk assessment. The model categorizes elements into two main groups: Motivational Elements and Plan Elements.
To effectively assess risk, one must first understand the specific constructs within the model:
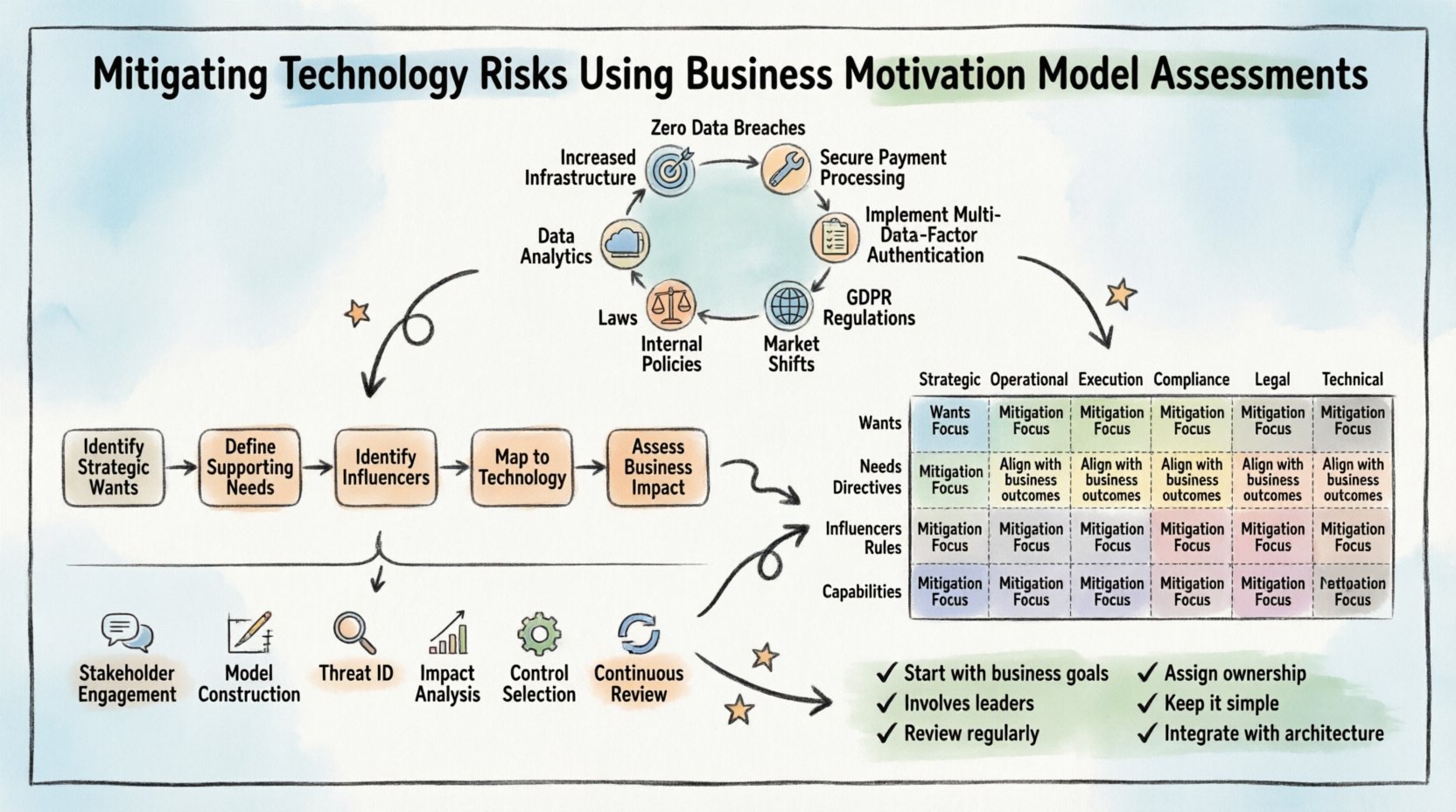
- Wants: These are the desired outcomes. They represent the goals or objectives the organization seeks to achieve. In a risk context, a Want might be “Increased Market Share” or “Zero Data Breaches.” If a technology risk threatens a specific Want, it is immediately flagged as a priority.
- Needs: These are the things required to satisfy the Wants. A Need is often a capability, a resource, or a process. For example, if the Want is “Customer Trust,” the Need might be “Secure Payment Processing.” Risks associated with the fulfillment of Needs are operational risks.
- Directives: These are the plans or actions taken to satisfy Needs. Directives guide the execution of strategy. A Directive could be “Implement Multi-Factor Authentication.” If a Directive is poorly executed or fails, the associated risk materializes.
- Influencers: These are external or internal factors that affect the ability to achieve Wants or satisfy Needs. Influencers include regulations, market conditions, or competitor actions. Regulatory changes are a common source of technology risk.
- Rules: These are constraints that must be followed. Rules can be mandatory (laws) or voluntary (internal policies). Violating a Rule is a direct compliance risk.
- Capabilities: These are the abilities of the enterprise to perform actions. Technology capabilities, such as cloud infrastructure or data analytics, are critical assets that carry inherent risks if not properly managed.
When assessing technology risks, the BMM shifts the focus from “what could break” to “what could prevent us from achieving our goals.” This perspective ensures that risk management efforts are always tied back to business value.
🎯 Connecting Motivation to Risk Identification
The core strength of using BMM for risk mitigation lies in its ability to trace threats back to motivations. Traditional risk assessments often start with an asset inventory. While useful, this method can miss the strategic context. A BMM-based assessment starts with the business motivations and works downward to the technology layer.
The Risk Mapping Process
Mapping risk to motivation involves a systematic flow:
- Identify Strategic Wants: List the top-level goals. Examples include “Expand to International Markets” or “Reduce Operational Costs by 15%.”
- Define Supporting Needs: Determine what is required to achieve these goals. To expand internationally, you might need “Compliant Data Residency” or “Localized Payment Gateways.”
- Identify Potential Influencers: What could stop these Needs from being met? For data residency, the influencer might be “New GDPR Regulations.” For payment gateways, it might be “Vendor Instability.”
- Map to Technology Capabilities: What technology supports the Needs? This is where the specific risk surfaces. If the capability is “Cloud Storage,” the risk is “Data Leakage” or “Service Outage.”
- Assess Impact on Motivation: If the risk occurs, how does it affect the original Want? Does it prevent expansion? Does it increase costs?
This top-down approach prevents the common pitfall of securing assets that do not support critical business outcomes. It ensures resources are allocated to protect the things that matter most.
📊 Risk Categories Mapped to BMM Elements
Different types of risks align with different elements of the Business Motivation Model. Understanding these alignments helps in categorizing threats and selecting appropriate mitigation strategies. The table below illustrates common risk types and their corresponding BMM elements.
| BMM Element | Associated Risk Type | Mitigation Focus |
|---|---|---|
| Wants (Goals) | Strategic Risk | Ensure technology alignment with vision. Diversify investments. |
| Needs (Resources) | Operational Risk | Redundancy, capacity planning, and supply chain resilience. |
| Directives (Plans) | Execution Risk | Project management controls, change management, and testing. |
| Influencers (Environment) | Compliance/Regulatory Risk | Continuous monitoring of laws, standards, and market shifts. |
| Rules (Constraints) | Legal/Policy Risk | Automated policy enforcement and audit trails. |
| Capabilities (Assets) | Technical/Security Risk | Vulnerability management, access controls, and encryption. |
By using this matrix, risk managers can ensure they are not overlooking specific categories. For instance, a heavy focus on Technical Risk might lead to neglecting Strategic Risk, where a technology investment fails to support the long-term vision.
🔄 Implementation Framework for Assessments
Implementing a BMM-based risk assessment does not require new software or complex overhauls. It requires a change in thinking and process. The following steps outline a practical approach to integrating this model into existing risk management workflows.
1. Stakeholder Engagement
Begin by engaging business leaders, not just IT staff. The BMM relies on accurate business input. Interview stakeholders to understand their primary Wants and Needs. Ask questions such as:
- What are the top three business outcomes for the next fiscal year?
- What dependencies do you have on technology to achieve these outcomes?
- What external factors worry you the most regarding our technology strategy?
This phase establishes the baseline for the assessment. Without accurate business input, the risk model will be disconnected from reality.
2. Model Construction
Create a visual representation of the business motivation for the specific domain being assessed. This could be a diagram or a structured document. Place the primary business Goals at the top. Below them, list the Needs and Capabilities. Connect them to show dependencies. This visual aid serves as a map for risk identification.
3. Threat Identification
Review each link in the model. For every Capability, ask what could go wrong. For every Directive, ask what could cause failure. For every Rule, ask what could lead to violation. Document these as potential risks. At this stage, do not worry about mitigation; focus on identification.
4. Impact Analysis
Once risks are identified, assess their impact on the Motivational Elements. Does a security breach impact a specific Want? Does a system outage impact a Need? Use a scoring system to prioritize. Risks that threaten high-priority Wants should receive the most attention and resources.
5. Control Selection
Select controls that directly address the identified risks. Because the model links risks to business motivations, the controls selected will inherently support business goals. For example, if the Want is “High Availability,” a control like “Multi-Region Deployment” is directly relevant. If the Want is “Data Privacy,” controls like “Encryption at Rest” are relevant.
6. Continuous Review
Business motivations are not static. Goals change, regulations update, and technology evolves. The BMM assessment must be a living process. Schedule regular reviews to update the model. If a business goal is retired, the associated risks should be re-evaluated or removed from the active register.
⚖️ Governance and Continuous Monitoring
Once the assessment is complete, governance ensures that the mitigations remain effective over time. Technology risk is dynamic, and static assessments quickly become obsolete. A robust governance structure is required to maintain the alignment between business motivation and risk posture.
Key Governance Activities
- Periodic Re-assessment: Conduct formal BMM reviews quarterly or biannually. This ensures that any shifts in business strategy are reflected in the risk profile.
- Change Management Integration: When a new technology capability is proposed, it must be evaluated against the BMM. Does it support a Want? Does it introduce new Influencers? This prevents shadow IT from creating unmanaged risk.
- Risk Ownership: Assign ownership of risks to business leaders, not just IT. If a risk affects a specific business Want, the business leader should own the decision to accept or mitigate that risk.
- Reporting Metrics: Develop metrics that report on risk status relative to business goals. Instead of reporting “Number of Vulnerabilities,” report “Risk Exposure to Strategic Goals.”
🧩 Common Pitfalls to Avoid
While the Business Motivation Model offers significant benefits, organizations often stumble during implementation. Being aware of these common pitfalls can help teams navigate the process more effectively.
- Over-Complication: Do not attempt to model every single business goal. Focus on the critical drivers of risk. A model that is too complex will be ignored by stakeholders.
- Ignoring the Influencers: Many assessments focus heavily on internal capabilities and neglect external Influencers. Market shifts and regulatory changes are often the biggest sources of technology risk.
- Lack of Business Buy-in: If the business does not own the model, it will not be maintained. Ensure that business leaders are actively involved in defining the Wants and Needs.
- Static Thinking: Treating the assessment as a one-time project rather than an ongoing process. Technology risk changes faster than the assessment cycle.
- Disconnection from Architecture: The BMM should feed into the Enterprise Architecture. If the risk model exists in a silo, it will not influence technical design decisions.
🚀 Future-Proofing the Strategy
The landscape of technology risk is evolving rapidly. Emerging technologies such as artificial intelligence, quantum computing, and decentralized networks introduce new vectors of risk. A BMM-based approach provides the flexibility needed to adapt to these changes.
As new technologies emerge, they should be evaluated against the existing BMM structure. Does this new capability support a current Want? Does it create a new Need? If a new Want emerges, such as “AI-Driven Decision Making,” the risk model must expand to include risks associated with algorithmic bias and data integrity.
Furthermore, the BMM encourages a holistic view. It does not isolate security from operations or strategy. This integration is crucial for modern risk management. By keeping the business motivation at the center, organizations can ensure that their technology investments remain resilient against both current and future threats.
📈 Measuring Success and Value
How do you know if the BMM risk assessment is working? Success is measured by the alignment between risk posture and business outcomes. Look for indicators such as:
- Reduced Incident Response Time: When risks are mapped to specific goals, response teams understand the business priority faster.
- Better Resource Allocation: Budget is directed toward protecting high-value business assets rather than generic IT infrastructure.
- Improved Stakeholder Communication: Business leaders can understand risk reports because they are framed in terms of their own goals.
- Agility in Risk Management: The organization can adapt risk strategies quickly as business priorities shift.
Ultimately, the goal is to move from a reactive stance to a proactive one. By understanding the motivations that drive the business, risk professionals can anticipate problems before they occur. This proactive stance reduces the likelihood of disruption and supports sustainable growth.
🛠️ Summary of Best Practices
To conclude this guide, here is a concise list of best practices for implementing BMM in risk mitigation:
- Start with business goals, not technical assets.
- Involve business leaders in the modeling process.
- Use the table framework to categorize risks.
- Review the model regularly as business conditions change.
- Assign risk ownership to the business side.
- Keep the model simple and focused on critical drivers.
- Integrate the model with Enterprise Architecture.
- Report on risk impact to business outcomes.
By adhering to these practices, organizations can build a robust defense against technology risks. The Business Motivation Model offers a structured, logical way to ensure that risk management serves the business, rather than hindering it. In an era where technology is the backbone of enterprise operations, this alignment is not optional; it is essential for survival and success.
Adopting this framework requires discipline and commitment, but the payoff is a resilient organization capable of navigating complexity with confidence. The path forward involves continuous learning and adaptation, ensuring that the business remains motivated and secure in an ever-changing digital world.